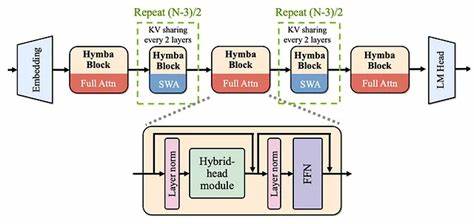
China has officially entered the global AI race with a groundbreaking announcement shaking up the…
The world of artificial intelligence is becoming more dramatic and threatening day by day, with…
Big News! the latest achievement for Artificial Intelligence, the Royal Swedish Academy of Sciences has…
OpenAI, a leading artificial intelligence research lab, has recently raised $6.6 billion in a new…
NVIDIA’s GeForce RTX 40 Series laptops are here to revolutionize how you learn, play, and…
00 /00